Network Monitoring Statement for 5038196576, 699603522, 120132402, 1908996000, 120024024, 8447891750

The network monitoring statement for identifiers 5038196576, 699603522, 120132402, 1908996000, 120024024, and 8447891750 provides essential insights into their operational metrics. Performance analyses reveal inconsistencies in response times and data integrity. Additionally, recent evaluations have identified vulnerabilities that require immediate remediation. Understanding these factors is crucial for optimizing network efficiency and security. The implications of these findings may shape future strategies for risk mitigation and operational resilience.
Overview of Network Nodes
Network nodes serve as critical components within a digital infrastructure, facilitating communication and data exchange across a network.
Various node types, including routers, switches, and servers, operate using standardized communication protocols to ensure seamless interactions.
Each node type plays a specific role, optimizing bandwidth usage and enhancing data flow, thereby supporting an environment conducive to free and efficient information dissemination.
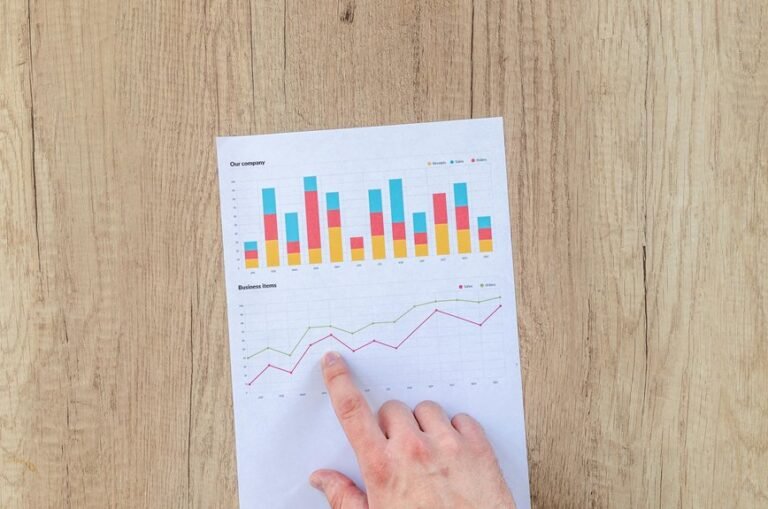
Performance Analysis of Unique Identifiers
Unique identifiers (UIDs) are essential for the efficient management and tracking of data across network environments.
Unique identifier analysis focuses on evaluating performance metrics such as response time, data integrity, and throughput. By assessing these metrics, organizations can optimize UID implementations, ensuring robust data flow and accessibility.
This analytical approach enables the identification of strengths and weaknesses within network infrastructures, fostering operational efficiency and data reliability.
Identifying Vulnerabilities and Risks
How can organizations effectively identify vulnerabilities and risks within their network systems?
Conducting a thorough vulnerability assessment is essential for uncovering potential threats. By employing advanced scanning tools and regular audits, organizations can pinpoint weaknesses.
Subsequently, effective risk mitigation strategies should be implemented, prioritizing remediation efforts based on the severity of identified vulnerabilities, thereby enhancing the overall security posture and resilience of the network infrastructure.
Best Practices for Network Optimization
Effective network security measures must be complemented by best practices for network optimization to ensure both performance and reliability.
Implementing bandwidth management techniques allows organizations to allocate resources effectively, preventing congestion.
Additionally, traffic shaping can prioritize critical applications, enhancing overall user experience.
Conclusion
In conclusion, the network monitoring analysis of identifiers 5038196576, 699603522, 120132402, 1908996000, 120024024, and 8447891750 reveals a landscape fraught with both performance challenges and security vulnerabilities. Like a ship navigating turbulent waters, these nodes require strategic optimization and robust risk mitigation to ensure resilience. By implementing best practices and continuous monitoring, organizations can fortify their network infrastructure, enhancing operational efficiency and safeguarding against potential threats.