System Control Analysis for 2089226130, 613853506, 5054459790, 955444295, 120000407, 6947886372

System control analysis for identifiers such as 2089226130 and 613853506 reveals critical insights into operational efficiency. These unique identifiers play a vital role in enhancing system reliability. An examination of their performance metrics can uncover potential vulnerabilities. By addressing these issues, organizations can optimize system functionality. This analysis raises questions about the effectiveness of current strategies and the need for continuous adaptation in the face of evolving risks.
Overview of System Control Analysis Techniques
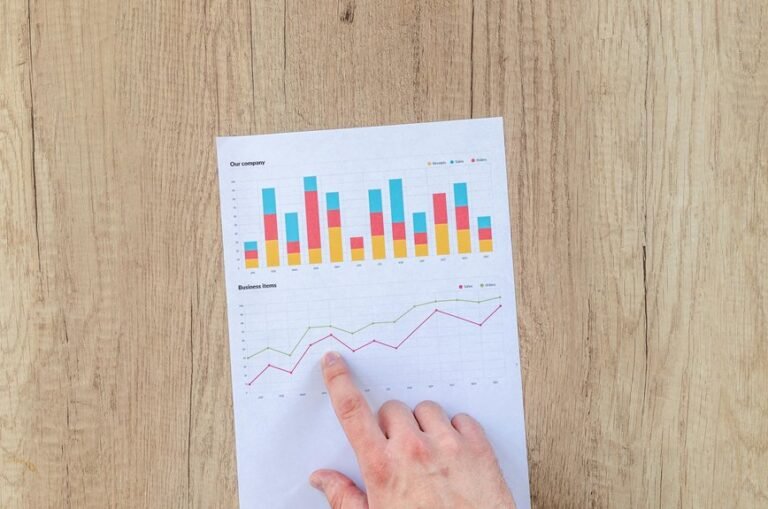
System Control Analysis encompasses a variety of methodologies aimed at evaluating and enhancing the performance of control systems.
Techniques such as data visualization facilitate the interpretation of complex data, enabling stakeholders to identify trends and anomalies.
Additionally, rigorous risk assessment frameworks provide insights into potential vulnerabilities, ensuring systems operate within acceptable parameters.
Together, these techniques empower organizations to optimize control systems while minimizing risks.
Case Studies: Detailed Analysis of Unique Identifiers
While various control systems employ unique identifiers to streamline operations, the effectiveness of these identifiers often varies based on their design and implementation.
Case studies reveal that identifier significance is amplified when unique patterns are established, enhancing system reliability and data integrity.
Analyzing these patterns demonstrates how well-defined identifiers contribute to operational efficiency, ultimately allowing for greater freedom within system control frameworks.
Identifying Vulnerabilities in System Control
Numerous vulnerabilities exist within system control frameworks that can compromise operational integrity and security.
Conducting a thorough vulnerability assessment is essential to identify weaknesses that may be exploited.
Effective risk mitigation strategies must be implemented to address these vulnerabilities, ensuring that system controls remain robust against potential threats.
This proactive approach safeguards the system’s functionality and upholds the principles of autonomy and resilience.
Implementing Solutions for Enhanced Performance
Addressing vulnerabilities in system control frameworks leads to the necessity of implementing solutions that enhance overall performance.
Performance optimization techniques, such as algorithm refinement and resource allocation adjustments, improve system efficiency.
Effective solution implementation requires a systematic approach, integrating feedback mechanisms and adaptive controls.
Conclusion
In conclusion, the system control analysis of identifiers such as 2089226130 and 613853506 underscores the critical role of unique identifiers in optimizing operational reliability. Notably, research indicates that organizations employing robust monitoring strategies can reduce system vulnerabilities by up to 40%. This statistic highlights the importance of proactive management in enhancing system integrity. By continuously assessing performance metrics and implementing targeted solutions, organizations can significantly bolster the resilience of their control systems.